
Vigilant
Threat Intellignece
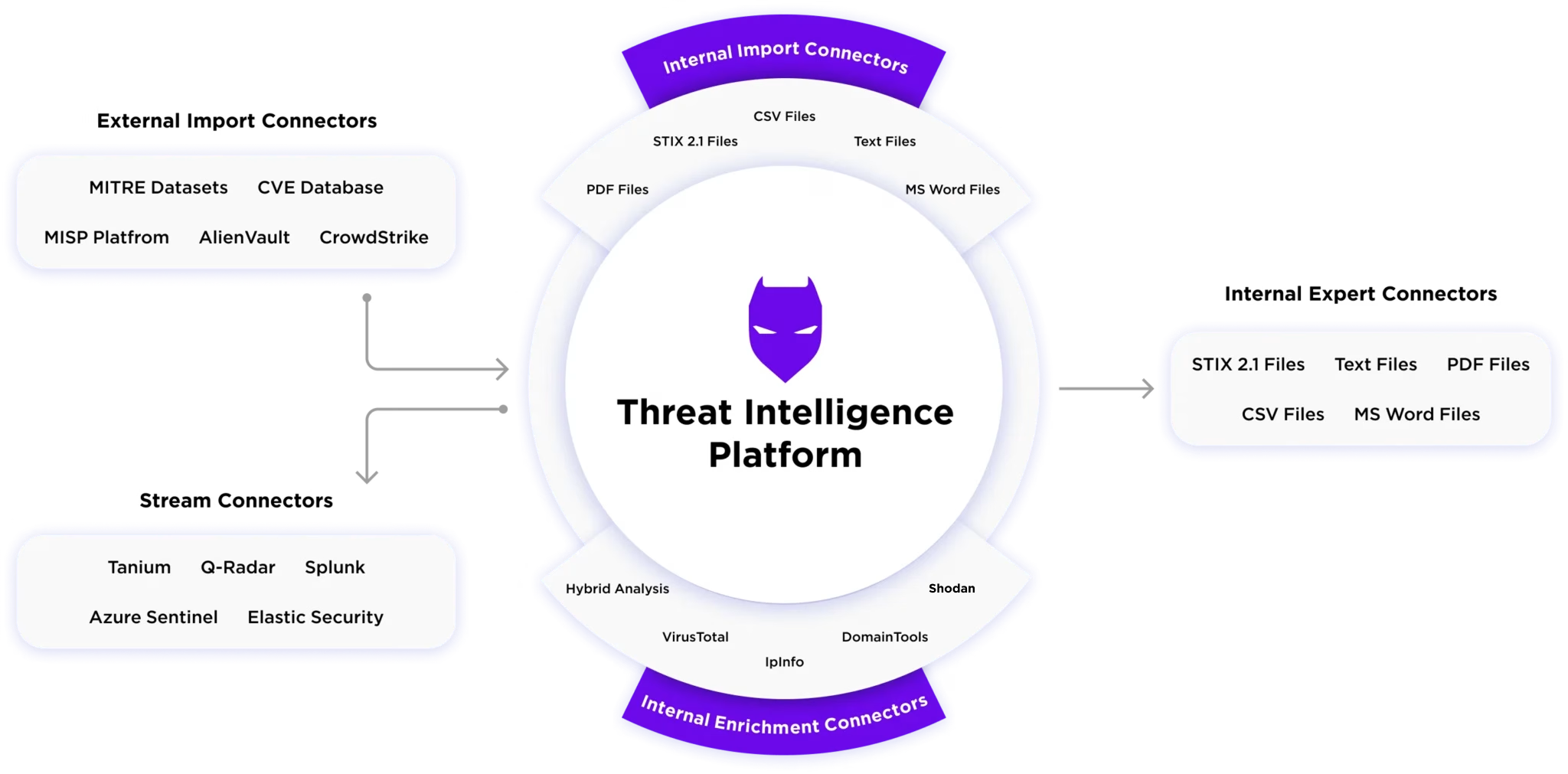
Our Threat Intelligence Feature provides you with the knowledge and tools to detect, analyze, and respond to these threats before they impact your business. With a focus on proactive defence
Maximize the benefits of your Threat Intelligence.
provides contextualized threat intelligence by linking related events and activities into a single, coherent narrative. This helps security teams understand the full scope of an attack, from initial entry to lateral movement and impact.

Live Threat Maps provide a visual representation of global threats in real time. This feature allows security teams to monitor active attacks worldwide and correlate them with their own environment.
provides real-time updates on known malware, ransomware, and other threats. It includes detailed information about threat actors, attack patterns, and indicators of compromise (IOCs).

Proactive Intelligence for Comprehensive Protection of Your Business from Cyber Threats
Leverage Cutting-Edge Threat Intelligence to Elevate Detection, Investigation, and Incident Response Capabilities
Proactive Defense with Intelligence
Proactively detect and neutralize emerging threats with AI-driven intelligence and automated XDR response—freeing analysts for strategic decisions
Detailed Threat Attribution
Associate incidents with particular threat actors, malware types, and active campaigns to better understand their impact on your organization
Real-Time Threat Assessment
Rapidly detect and address threats as they occur, empowering you to concentrate on urgent issues and reduce potential risks
The Power of Threat Intelligence.
Leverage Cutting-Edge Threat Intelligence to Elevate Detection, Investigation, and Incident Response Capabilities
Real-Time Data Feeds
An XDR solution with integrated Threat Intelligence leverages continuous real-time data streams. These feeds are sourced from a variety of trusted providers, ensuring that the intelligence is up-to-date and relevant to the latest attack vectors.
Automated Incident Response Mechanisms
Enables predefined responses to specific threat detections, such as isolating affected systems or blocking malicious traffic, to contain threats swiftly.
Massive Threat Library
Vigilant Threat Intelligence aggregates security data from endpoints, networks, cloud applications, and third-party sources.
Proactive Defense and Remediation
With actionable insights provided by Threat Intelligence, organizations can adopt a proactive approach to cybersecurity. By anticipating attack trends, teams can fortify defenses, quickly isolate compromised assets, and implement remediation strategies before significant damage occurs.
Secure your business with DeepSafer
Experience unrivaled cybersecurity protection with DeepSafer, an advanced AI-driven solution that safeguards your digital assets from evolving threats.

